One of the biggest benefits of moving your data to the cloud via Microsoft SharePoint Online and OneDrive for Business is the increase in accessibility. For security conscious companies that work with sensitive material, this is also one of the biggest concerns. If your data is no longer only accessible from restricted PCs and kept behind a corporate firewall, how can control where it’s being downloaded to?
I previously wrote about the use of Data Loss Prevention (DLP) policies to prevent data leaks via e-mail. This feature also can stop the upload of data with sensitive information to SharePoint or OneDrive all together. You may just want to ensure that the data that is stored in Microsoft’s cloud stays there. This is a task that can be easily accomplished via a Conditional Access policy that will prevent the download of files from cloud apps.
Configuring a Conditional Access Policy
Before proceeding with the policy configuration, be aware that the prerequisites for enforcing this are: Azure AAD P1 licensing and having your devices hybrid Azure AD joined, and/or being flagged as compliant in InTune, Microsoft’s MDM, as well as an E5 license. If your environment meets these requirements, let’s proceed to configuring a new Conditional Access policy.
- From Azure Active Directory open Enterprise Applications > Conditional Access > +New policy
- Give your new policy a Name
- Select Users and groups and on the Include tab, select All users. On the Exclude tab, select Directory Roles and select Global Administrators.
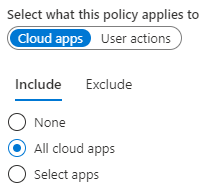
- Select Cloud apps or actions and select All cloud apps on the Include tab.
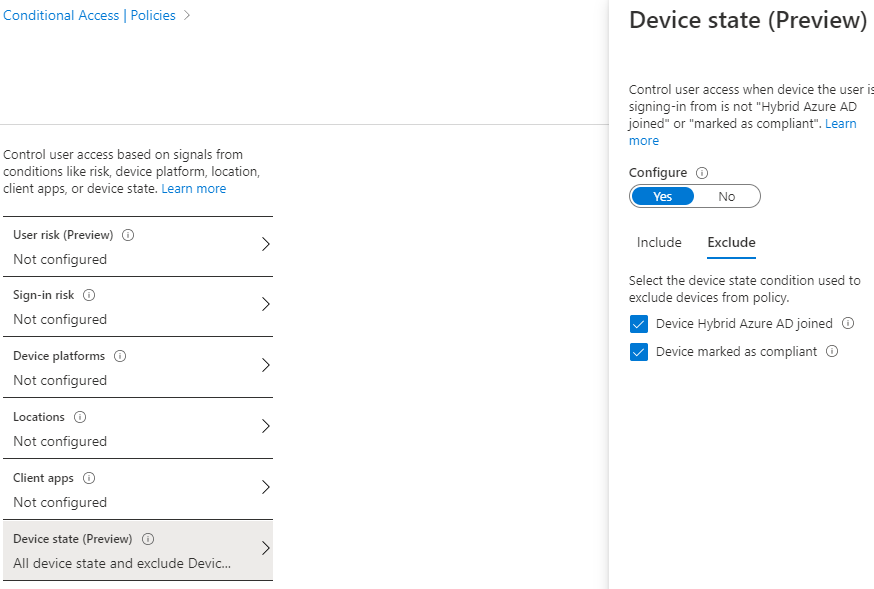
- Select Conditions > Devices state, click Yes under Configure. On the Exclude tab, select Device Hybrid Azure AD joined and/or Device marked as compliant.
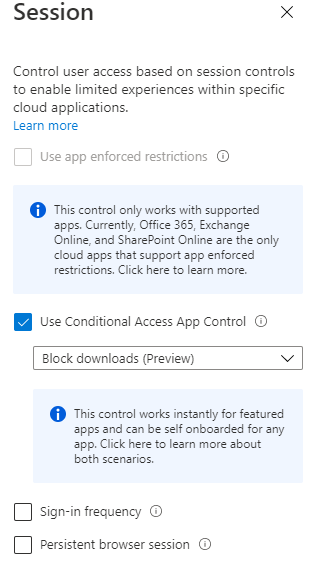
- Select Session and check Use conditional Access App Control, from the drop down select Block downloads.
- Set the Enable policy to On and then click Create.
What’s next?
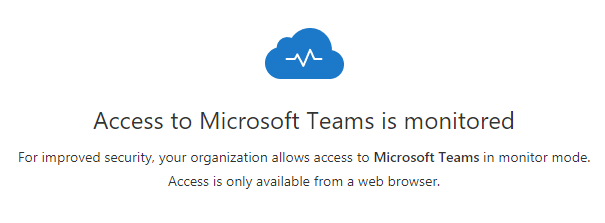
The policy is now active and being enforced against all users, except those with a Global Administrator role in Office 365. When a user goes to access a cloud application via the web, such as Microsoft Teams, they will see the below warning upon sign-in:
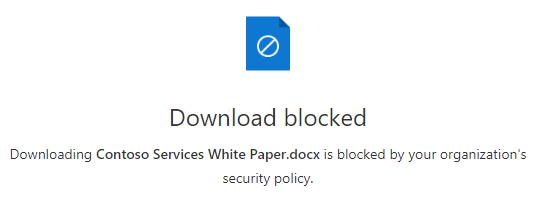
When they attempt to download a file, the below prompt is given, and the download is prevented:
Microsoft accomplishes this by controlling user sessions via redirecting them through a reverse proxy instead of directly to the web app. This allows for real time monitoring and enforcement of session policies. Additional policies can be used to further the restrictions in place, such as using an App Control Policy to prevent the copying and pasting of information from documents accessed from the cloud. We will look at this type of policy in a future post.
Have any questions about setting up a Conditional Access policy to protect your company’s data? Please contact us at any time!
This publication contains general information only and Sikich is not, by means of this publication, rendering accounting, business, financial, investment, legal, tax, or any other professional advice or services. This publication is not a substitute for such professional advice or services, nor should you use it as a basis for any decision, action or omission that may affect you or your business. Before making any decision, taking any action or omitting an action that may affect you or your business, you should consult a qualified professional advisor. In addition, this publication may contain certain content generated by an artificial intelligence (AI) language model. You acknowledge that Sikich shall not be responsible for any loss sustained by you or any person who relies on this publication.









