This website uses cookies so that we can provide you with the best user experience possible. Cookie information is stored in your browser and performs functions such as recognising you when you return to our website and helping our team to understand which sections of the website you find most interesting and useful.
- Audit and Assurance
- Business Succession Plan
- Business Transformation
- Cloud Services
- Consulting Services
- CRM and ERP Products
- CRM Services
- Cybersecurity
- Data and Analytics
- ERP Services
- Forensic and Valuation
- Governance, Risk and Compliance
- HEADSTART Implementations
- Human Capital Management and Payroll
- Insurance Services
- Internal Audit
- Contact
- Services
- Audit & Assurance
- Business Succession Plan
- Business Transformation
- Cloud Services
- Consulting Services
- CRM and ERP Products
- CRM Services
- Cybersecurity
- Data and Analytics
- ERP Services
- Forensic & Valuation
- Governance, Risk and Compliance
- HEADSTART Implementations
- Human Capital Management & Payroll
- Insurance Services
- Internal Audit
- Investment Banking
- Lender Services
- IT and Managed Services
- Marketing and Communications
- Modern Workplace
- Outsourced Accounting
- Regulatory, Quality & Compliance
- Site Selection & Incentives
- Spend Management
- Tax
- Transaction Advisory
- Wealth Management
- Workforce Risk Management
- Industries
- Construction & Real Estate
- Discrete Manufacturing
- Federal Government
- Financial Services
- Government Contractors
- Industrial Equipment Manufacturing
- Life Sciences
- Manufacturing and Distribution
- Not-for-profit
- Process Manufacturing
- Professional Services
- Rolled Products
- State & Local Government
- Title IV Audit & Consulting
- Distribution & Supply Chain
- Insights
- About
- Locations
- Careers
- Pay
What You Need to Know About the Netlogon Vulnerability
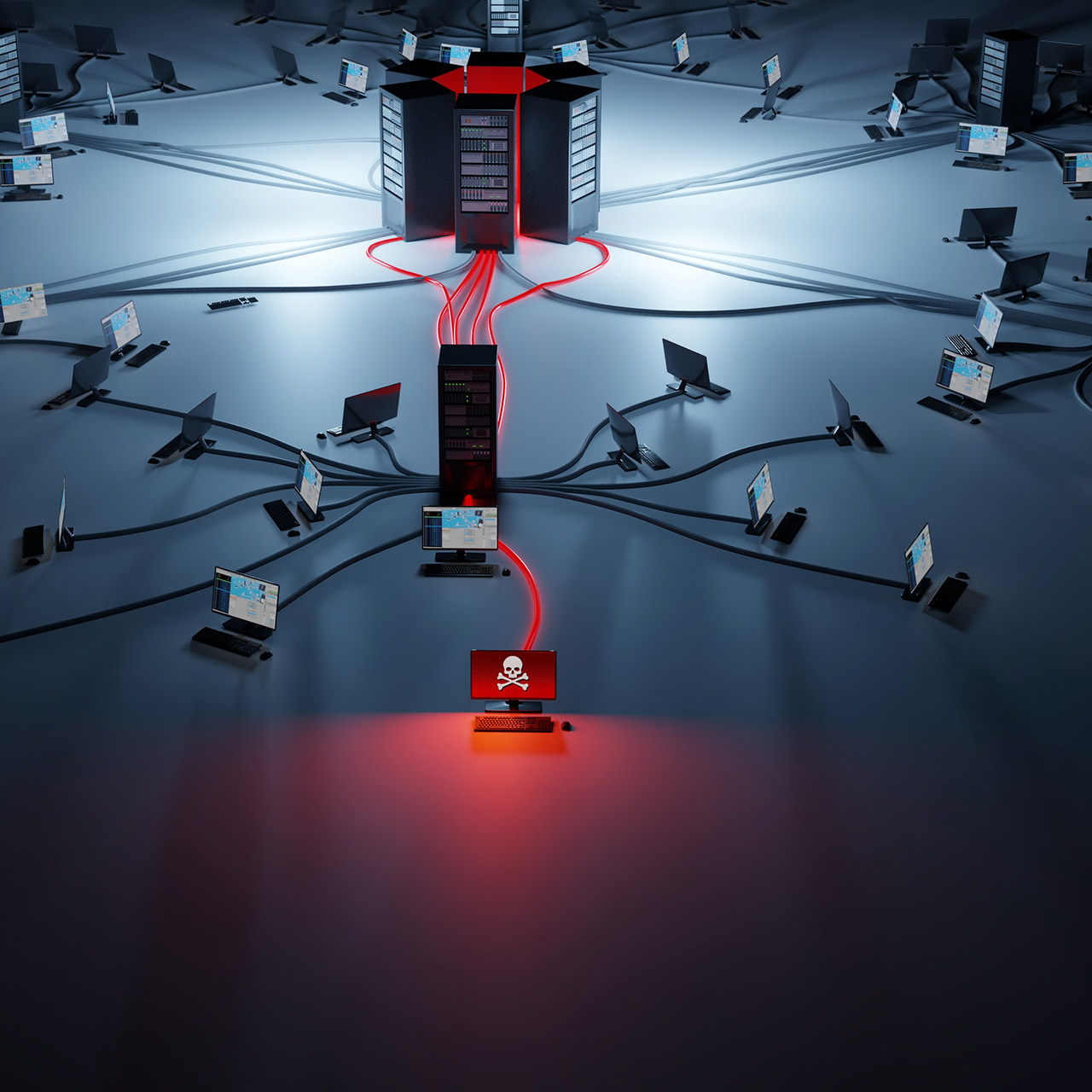
Last month, as part of their monthly rollup, Microsoft released a fix for CVE-2020-1472, a critical vulnerability in Netlogon that allows elevation of privileges. This weekend, exploit code for this vulnerability became available that shows how damaging it can be.
The flaw in Netlogon allows an unauthenticated attacker on an internal network to connect to the domain controller and set a new computer password. The attacker can then use this new password to take over the domain controller and, from there, gain control of the Windows network. Since an attacker would generally need to be on your internal network to communicate with the domain controller to run the attack, attacks from the Internet should be limited.
Microsoft hasn’t yet identified any mitigations or workarounds beyond applying the August 2020 rollup patch. If you haven’t already, you should work to apply the patches to your servers as soon as possible.
Should you have any questions about applying patches or protecting your systems, please reach out to our team and we’ll be happy to help.
This publication contains general information only and Sikich is not, by means of this publication, rendering accounting, business, financial, investment, legal, tax, or any other professional advice or services. This publication is not a substitute for such professional advice or services, nor should you use it as a basis for any decision, action or omission that may affect you or your business. Before making any decision, taking any action or omitting an action that may affect you or your business, you should consult a qualified professional advisor. In addition, this publication may contain certain content generated by an artificial intelligence (AI) language model. You acknowledge that Sikich shall not be responsible for any loss sustained by you or any person who relies on this publication.
About the Author
Sikich
Sikich is a global company specializing in technology-enabled professional services. With more than 1,900 employees, Sikich draws on a diverse portfolio of technology solutions to deliver transformative digital strategies and is comprised of one of the largest CPA firms in the United States. From corporations and not-for-profits to state and local governments and federal agencies, Sikich clients utilize a broad spectrum of services* and products to help them improve performance and achieve long-term, strategic goals. *Securities offered through Sikich Corporate Finance LLC, member FINRA/SIPC. Investment advisory services offered through Sikich Financial, an SEC Registered Investment Advisor.
Sign up for Insights
Join 14,000+ Business executives and decision makers.
Latest Insights
Life Science
Tech Challenges in the Phases of Life Sciences Organizations...
July 26, 2024
News
Sikich India Welcomes Siddharth Sharma as Human Resources Di...
July 25, 2024
Not-for-Profit
Compliance Supplement and Uniform Guidance Changes to Know
July 25, 2024
Accounting
Ryan Spohn Featured in Accounting Today
July 25, 2024
Sikich On Demand
On Demand – 2024 Yellowbook Webinar Series: Session 5 ...
July 24, 2024
Dynamics 365
How Manufacturing Can Embrace Change Through Digital Transfo...
July 24, 2024
Security
KnowBe4: Security Awareness
July 23, 2024
Construction
Construction Industry Outlook: A Q&A
July 19, 2024
Not-for-Profit
Demystifying the Current Expected Credit Loss Model for Not-...
July 19, 2024
Sikich On Demand
On Demand – 2024 Yellowbook Webinar Series: Session 6 ...
July 19, 2024




